Ping tcp command in the Cisco ASA firewall - Duration: 3:50. Nat0.net 6,121 views. Piping and Filtering Command Output: Intro to ASA Firewalls: Cisco Training Videos - Duration: 3:23. Jun 17, 2014 ping tcp command in the Cisco ASA firewall - Duration: 3:50. Nat0.net 6,121 views. Piping and Filtering Command Output: Intro to ASA Firewalls: Cisco Training Videos - Duration: 3:23. This includes ASA and IOS operating systems. You can however do a ping for a VERY long time by indicating a lot of pings. Ping 192.168.1.1 repeat 9999999. Or if the repeat command is unavailable use the extended ping by simply issuing the ping command by itself and follow the prompts after. If that still isn’t good enough, you can set up an. And you can ping the interface ip address of the interface 'pointing to you' (if it is allowed by an 'icmp permit' statement), but the ASA will never allow to ping that interface ip address from hosts behind other interfaces of the ASA (except if the ASA interface is configured as 'management interface' or for 'management access').
Sadly enough, sometimes network equipment goes out of order. This, of course, happens when you’re least expecting it. In most cases that I’ve come across throughout my work, this is what happens: Cisco ASA is unexpectedly powered down or reloaded (due to planned or unplanned power outage, thunderstorm or work with electric equipment), and after reload, the interfaces, VPN tunnels and other services don’t come back up. We’re not going to examine the situation in which the device cannot turn on entirely and all the LED indicators are dead – in that case, a replacement for the device is the only viable option. Let’s focus on the situation when the Cisco ASA device is still operable, but does not perform a full load – i.e. the Cisco IOS operating system image can’t load properly. In this case, there is still a chance to reanimate the device, at least until you get a new one for replacement.
The first thing we need to do is connect to the firewall through a console cable. If the firewall does not respond to any commands and produces no output on the console screen, then you’ve reached the worst-case scenario – you can thank the device for its long and fruitful service and put it on a shelf. However, if you are seeing some activity on the console screen, it’s not that bad and you can try to understand what’s going on. The firewall may have entered into the special ROMMON mode (under normal circumstances, this mode is activated by pressing the ESC key during boot-up) or is in a cyclic reload that happens as it tries to load the operating system image.
The special ROMMON mode looks something like this:Use ? for help.
ROMMON #0>
Asa Ping Command Prompt
Once you’re in this mode, you should try to force the device to start by entering the system command “boot“:ROMMON #0>boot
Cisco ASA will try to load the operating system image that is located on the internal Flash memory. I can tell you right now that, in my years of practice, this has worked only once, when I got lucky and the device booted normally. Most of the times if the firewall does not load on its own, then it will not be able to load from the boot command under ROMMON mode.
In this case, let’s remember how Cisco devices work:
The operating system is located on some kind of nonvolatile memory and is loaded into RAM once, upon device boot-up. After that, the operating system works until the next reload. Flash memory is the most commonly used nonvolatile memory for storing the Cisco IOS (most likely you’re reading this article because it’s what went out of order), but you always have the option to specify some external resource that stores the IOS you need to load – for example, a TFTP server.
The task of recovering your firewall will come down to:
- installing a TFTP server on some workstation. Using a simple laptop will suffice.
- placing the relevant Cisco IOS on the TFTP server
- connecting one of the Cisco ASA interfaces directly to the workstation that has the TFTP server
- specifying that workstation as the IOS source and booting up the firewall with that image

In order to install TFTP server software, you simply need to download the install package, start the software, and copy the IOS image into the folder indicated in the software’s dialog box.
I suggest using the simple and free TFTPD. You can download it here.
The interface of the program is extremely straightforward and should not cause any difficulties.
Place the IOS file for your firewall into the C:Program FilesTftpd64 folder that is specified in the “Current Directory” field. It is strongly advised to use the same IOS that was on the device when it went out of order. Don’t use a newer version until you are sure that your firewall works fine.
Important!
Note how the TFTP server software interface works: if the IP address of the laptop’s NIC gets changed, the “Server interfaces” field will still hold the old information. Check this and reload the TFTP server program if the value in that field is incorrect. For our example, we will use the address 192.168.1.2
Next, we need to connect the laptop’s LAN interface to the Ethernet 0/0 interface of the firewall with a straight-through patch cord.
Inside the firewall’s console (ROMMON mode) enter the IP address (ADDRESS), port number (PORT), TFTP server address (SERVER) and the operating system image file (IMAGE) information.
Important!
When entering the commands in ROMMON mode, you have to enter them in full – no abbreviations or short versions are available.rommon #1> ADDRESS=192.168.1.1
rommon #2> PORT=Ethernet0/0
rommon #3> SERVER=192.168.1.2
rommon #4> IMAGE=asa803-k8.bin
Important!
In this example the Cisco ASA firewall and the laptop with TFTP server software are directly connected to each other, so there is no need to specify the default gateway. However, if the corporate network is available, you can install the TFTP server on any network workstation and specify the default gateway (GATEWAY) and/or VLAN tag (VLAN) parameters in Cisco ASA‘s ROMMON:rommon #5> GATEWAY=Х.Х.Х.Х
rommon #6> VLAN=Y
Enter the IP address for the default gateway of your network instead of X.X.X.X. Enter the VLAN tag for your VLAN instead of Y.
You can check the values that you entered using the “set” command:rommon #7> set
The availability of the TFTP server is checked with the “ping server” command:rommon #8> ping server
Once you’ve ensured that the workstation with TFTP server software and Cisco ASA firewall are connected and configured correctly, enter the command “tftp” to start the process of loading the IOS:rommon #8> tftp
Important!
Even if your device loads successfully, I still suggest that you work on finding a replacement, since its reliability is now questionable.
To emphasize one more time: this article describes an emergency recovery of a Cisco ASA device and the success of the procedure depends on how badly the device’s components are damaged. Everything laid out in this article will 100% work if the hardware is intact.
This article was written by Alexey Yurchenko
Back to Table of contents
Most networking administrators have probably spent at least some time setting up a remote-access VPN for their company or for a customer. To authenticate end-users that connect to the VPN, it is very common to utilize an external database of users and to communicate with this external database you usually have to use the LDAP or RADIUS-protocol to talk either directly to an LDAP-catalog or to a RADIUS-server (like Cisco’s Identity Services Engine, ISE, for example).
However, if your VPN-solution consists of an Cisco ASA-firewall and the AnyConnect VPN software, there is a new option/protocol available to handle authentication: SAML, which stands for Security Assertion Markup Language. SAML has grown big in the last few years to provide authentication and single sign-on (SSO) experiences for applications like email, websites, ticket services and much more. The general idea of SAML is that once you have gone through a succesful authentication, you are handed a sort of cookie or “ticket” inside your web browser that will allow you to automatically be signed into the next service you want to use that also uses the same SAML-authentication. Today, there are many different products that use SAML-authentication from well-known companies like Microsoft, Okta, Ping Identity and even Cisco (through their Duo service).
As of this writing, successful SAML-authentications taking place for VPN does not “carry over” for use with other services because of how AnyConnect works… so keep that in mind for your own implementation.
I am not going to go into detail how SAML-authentication works but the main thing about the SAML-authentication flow is that when you initiate a VPN-session in AnyConnect (by typing in the URL/IP to your ASA and clicking “Connect”) instead of getting the normal AnyConnect login-prompt you will be redirected to a so called Identity Provider (IdP) which will present you with a login website that opens up inside AnyConnect (at least if you are using AnyConnect version 4.6 or newer). It is very common for companies and organizations to design their own login-page using their brand colors and logotypes to make users feel at home. Since the VPN login will look the same as for other applications used by the users, they will be very familiar with the interface. In SAML-terms the ASA will be acting as a Service Provider (SP).
This is not going to be a complete guide on how to setup SAML-authentication for VPN on the ASA, we will only cover the SAML-configuration on the ASA and not the configuration of basc VPN-settings like Group Policies etc. We will also not cover the configuration of the IdP, mainly because 1) you, the network administrator, will probably not be the one tasked to do that configuration and 2) there are way to many different IdP-services and I’ve barely seen any of them. This article is more about putting together a collection of good things to know that I’ve picked up from implementing SAML-authentication myself and from reading about other people’s experience on the Cisco Support forum. The main reason I felt the need to make this article is that Cisco’s own documentation regarding SAML is pretty barebone and it does not cover all the steps needed in a good enough manner, in my opinion.
General Setup
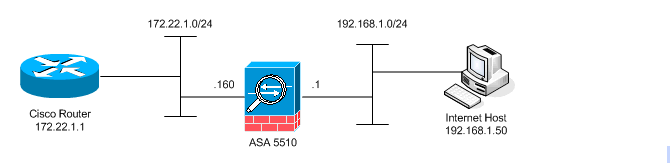
Below you see a simple diagram of the connections and communication that takes place in a SAML VPN-solution. The IdP could be either on your internal network, your DMZ or on the internet if you are using a cloud service.
Technical requirements
I’m just gonna get this out right away, there are some technical requirements that need to be met to use SAML-authentication for your VPN-connections:
Your ASA must have a trusted certificate installed, preferably from a third-party.
Your IdP must also have a trusted certificate installed, preferably from a third-party.
SAML-authentication differs quite a bit from the usual RADIUS or LDAP-authentication you are used to: the ASA doesn’t actually know the name of the user until the authentication is complete (either sucessful or failed) since the authentication takes place on the IdP. The IdP will inform the ASA of the username using the SAML-attribute NameID.
The Connection Profile (Tunnel Group) for your VPN that is going to use SAML as authentication method cannot contain any spaces. This it because the Connection Profile name is going to be used in the SAML-URL that the IdP will make use of. If you need to have multiple words in your Connection Profile, use dash or underscore between them.
If your SAML-authentication page is capable of reading user certificates from your computer, you must have AnyConnect version 4.7 or newer for this to work. Earlier version will not be able to fetch and present certificates stored on your computer to the IdP login page.
Your ASA must have DNS-servers configured that are able to do lookup the URL/IP of your Identity Provider servers.
Make sure your ASA and your IdP has NTP running and synchronized.


Basic VPN-configuration
Once again, this article assumes you have at least a decent amount of experience working with remote-access VPN configuration of an ASA and therefore I will not be covering the basics of Connection Profiles, Group Policies, IP-pools and so on. You know what’s best for your environment and the only thing this article will ask of you is to follow the technical requirement above (like the Connection Profile name) and that you set the Connection Profile’s User Authentication to SAML after you have configured the SAML (SSO) server futher down.
Adding the Identity Provider (IdP) certificate to the ASA
According to the documentation on Cisco’s website, you only need to add the root-certificate of the IdP’s certificate to the ASA buuut if you dig inside the Help pages inside the ASDM software you actually need to add the IdP’s certificate to the ASA.
As a best practice, I would recommend you install the root and intermediate certificates of the IdP’s certificate into the trusted certificate store of the ASA just in case. Head over to Configuration > Certificate Management > CA Certificates and click on Add to import the root certificate first and then do it again to import the intermediate certificate. You can add the certificates either as files (.der/.cer/.crt) or paste in the Base64 (text-version) of the certificates one by one.
However, for the “SAML-trust” to be setup between your ASA (SP) and the IdP, you also need to add the certificate of the IdP itself (the certificate that is used on the login website) as a trusted CA certificate.
Now comes the tricky part: I had trouble adding the IdP certificate itself in ASDM as a CA certificate because I kept getting an error stating the certificate could not be added because it needs to be added with the “no ca-check” command.
There is no way to issue the command “no ca-check” when importing the certificate using ASDM so you will need to add this certificate as a trustpoint using the command line instead.
<paste in the IdP-certificate in Base64-format>
And you’re done!
Configuring a SAML-server
Next up we need to add the SAML-server in ASDM, you can find the configuration for SAML-servers (or SSO-server as they are named here) under Configuration > Remote Access VPN > Clientless SSL VPN Access > Advanced > Single Signon Server. Don’t let the menu fool you, these servers are not only used for Clientless VPN.
The configuration of adding a SAML-server is pretty simple because there isn’t a lot of settings for you to play around with, but you will need to get some URLs from your IdP-administrator. Ask them for IDP Entity ID, Sign-in URL and Sign-out URL.
Please note that even the IDP Entity ID is a URL, it is not a “friendly name” that you can pick yourself so to speak.
Request Signature is something you must agree with your IdP-administrator about. Setting it to None is a very bad practice.
Request Timeout is something I would not touch unless told to by the IdP-administrator.
Make sure to remove “https://” before all URLs (except for the URL you set as IDP Entity ID) and all possibly added “/” from the end of the URLs, including the Base URL which is your ASA’s URL.
There is also a slight inconvenience with configuring SAML (SSO) servers and that is that everytime you make a change, you need to turn the SAML-configuration for that Connection Profile off and on again for the changes to take effect. Cisco is however aware of this oddity (it is tracked as en Enhancement under the bug-id CSCvi23605) and when you head into the SSO-server configuration you are greeted with this message:
To turn the SAML-configuration for a Connection Profile off and on again, either use the commands below or do it from ASDM on the Connection Profile > Basic > change SAML Identity Provider to “None” > click OK and Apply, then go back and reselect the SAML-server in the scroll list and click OK and Apply again.

Enter you Connection Profile/Tunnel Group:
Remove SAML-server from Connection Profile:
Re-add SAML-server to Connection Profile:
What the IdP-administrator will need from you
Your ASA certificate which is used on the “outside” interface of your ASA and for VPN-connections, they will need it to complete the trust between the ASA and the IdP.
Your SAML metadata which can be found if you (on the outside of the ASA) browse to the URL of your ASA and access the SAML-resource portion of your Connection Profile (the so-called metadata). For example, if your VPN URL is https://vpn.mydomain.com and your Connection Profile is called VPN-SAML-AUTH then your metadata-URL would be: https://vpn.mydomain.com/saml/sp/metadata/VPN-SAML-AUTH. You know the URL is correct if you get something like the image below if you browse to the URL. You can also get this information via the CLI using the command show saml metadata <Connection Profile name> which in my case would be show saml metadata VPN-SAML-AUTH.
Make sure to tell the IdP-administrator that you want the SAML-attribute NameID included in the SAML-response from the IdP when it tells the ASA if an authentication attempt was successful or not. If you do seperate authorization (via ISE for example), this will be the username that is sent to the authorization server. The NameID will also be what you, in the ASA, will see at the username for a remote-access VPN-session.
Agree upon what Request Signature to use and (optionally) a Request Timeout. A tips is to start by setting no Request Timeout on the ASA’s side and just let the IdP deal with this however it wants to to see if it just works right out of the box.
Making changes to the SAML-configuration on the ASA could change your SAML-metadata and the IdP-administrator might need to change something on their side as well, so always ask the IdP-administrator to verify that they have the latest metadata from your ASA.
Debugging SAML-authentication attempts
Your first few attempts of connecting to the SAML VPN is probably gonna go bad and then I would recommend this debug command to see if there is anything wrong with the SAML-connection from your ASA (the SP) and the IdP.
Using the debug above you get to see the actual creation of SAML-requests being sent between the ASA and the IdP. The 255 at the end is the debug level, with 255 providing you with the most output.
In my experience, I have run into trouble where the IdP has been trying to send SAML-attributes to the ASA that the ASA is not able to interpret or understand which would show up in the debugging log as:
Getmac Command
Here the SAML-attribute AuthnContextDeclRef is sent to the ASA from the IdP after authentication is successful, but the ASA does not know what this attribute is and therefore the VPN-authentication fails. If you run into this you pretty much have to ask your IdP administrator to make the IdP not send this attribute as there is no way to fix this on the ASA’s side due to the very limited SAML-configuration parameters of the ASA OS.
Cisco Asa Ping Source Address
Another trouble you could run into is that the clock of the ASA and the IdP is not synchronized or that the timeout for the SAML-tickets/sessions are not in agreement between the ASA and the IdP. This could happen if you define a Request Timeout in the ASA configuration for the SAML-server and the ASA tries to override the timeout values set by the IdP. This is what you could see in the debug then:
Drawbacks of using SAML
As of this writing (March 6th 2020) there is no easy way to apply different authorization rules for VPN users after they authenticate, like you would with Dynamic Access Policies (DAP) in ASA. The SAML-standard itself support many types of authorization parameters, but the ASA is unable to understand these. What you can do is let a separate authorization take place after the SAML-authentication, using either an LDAP-catalog or RADIUS-server, to get a second look at the user and then change authorization depending on group membership or account attributes, for example.
Asa Ping Command Server
Good luck!
